I’m still trying to figure that out too, unless the private key ships with the robot. Hopefully the W3C people get wise to reality, but I’m not holding my breath.
They don’t seem to understand that placing the joystick/gamepad behind a certificate paywall won’t solve the problem because the people who want to do the fingerprinting already have certificates. All it accomplishes is to make things difficult for everyone else.
The only other choice is to actually write a gamepad driver, (like nipple.js), that runs outside the context of the browser that a browser script can attach to or include, and completely avoids the gamepad browser API. But, as I mentioned in my objections, that’s like what the developer’s had to do back in the 1980’s when they had to capture the INT-19, (or whatever), vector to capture and control mouse inputs. I really do not want to do that, as it’s more trouble than it’s worth and it would be extremely joystick specific. (Not to mention requiring a software signing certificate and Microsoft approval before it could load a kernel driver in Windows.) I just don’t know how to pound it through their thick skulls that requiring a certificate to use the joystick is the WRONG answer.
What the certificate DOES do is it helps me avoid five minutes or so of navigating warning pages when I want to continue testing the robot.
It allows me to be somewhere else.
A wireless, (bluetooth), gamepad requires me to be in the immediate vicinity of the robot as the range is limited.
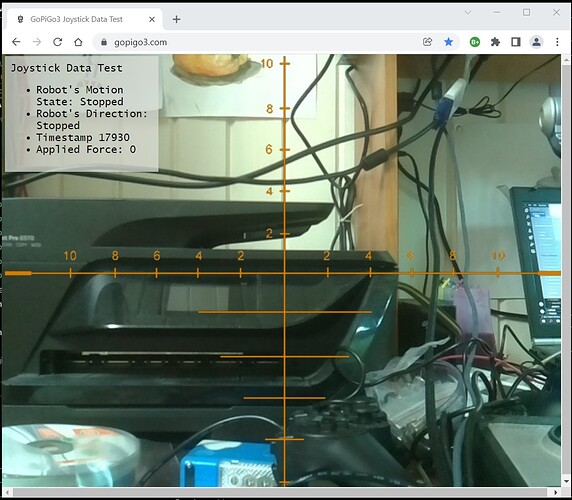
With my setup, I can be in front of my computer with a browser open, and the robot can be anywhere my WiFi reaches. Or, with a dynamic DNS arrangement, I can be anywhere and my robot can be anywhere else. If I were to attach a small 4G cellular card to the robot, and set the robot up for dynamic DNS, I could access it from anywhere I might happen to be. (i.e. under the house chasing a skunk out, while I am far, far away! I could have used the example of bomb sniffing but the skunk is a more likely scenario.  )
)
=====================
Update:
One of the big issues with using SSL with the Remote Camera Robot code is that there are TWO data streams:
- The web data stream which is the “plain vanilla” web traffic.
- The video data stream which shows the real-time video from the robot - which is being streamed from a different web server, (socketserver), on the 'bot.
The problem with that is the SSL connection only binds to the main web connection and not the video connection - and socketserver doesn’t support https connections.
One suggestion is nginx, configured as a “reverse proxy” which is like NAT traversal on a router. If this works the way they say it will, I can set up nginx as the https endpoint and have the un-encrypted streams sent to the existing infrastructure.
Let’s see what happens.